A large multinational counter-piracy operation has been conducted by the Pakistan-led Combined Task Force (CTF) 151 in the Gulf of Aden.
Focused Operation (FO) TAHAFFUZ was held from 26 February to 5 March, 2021, and was supported by assets from nine different nations with a shared objective to protect global maritime commerce.
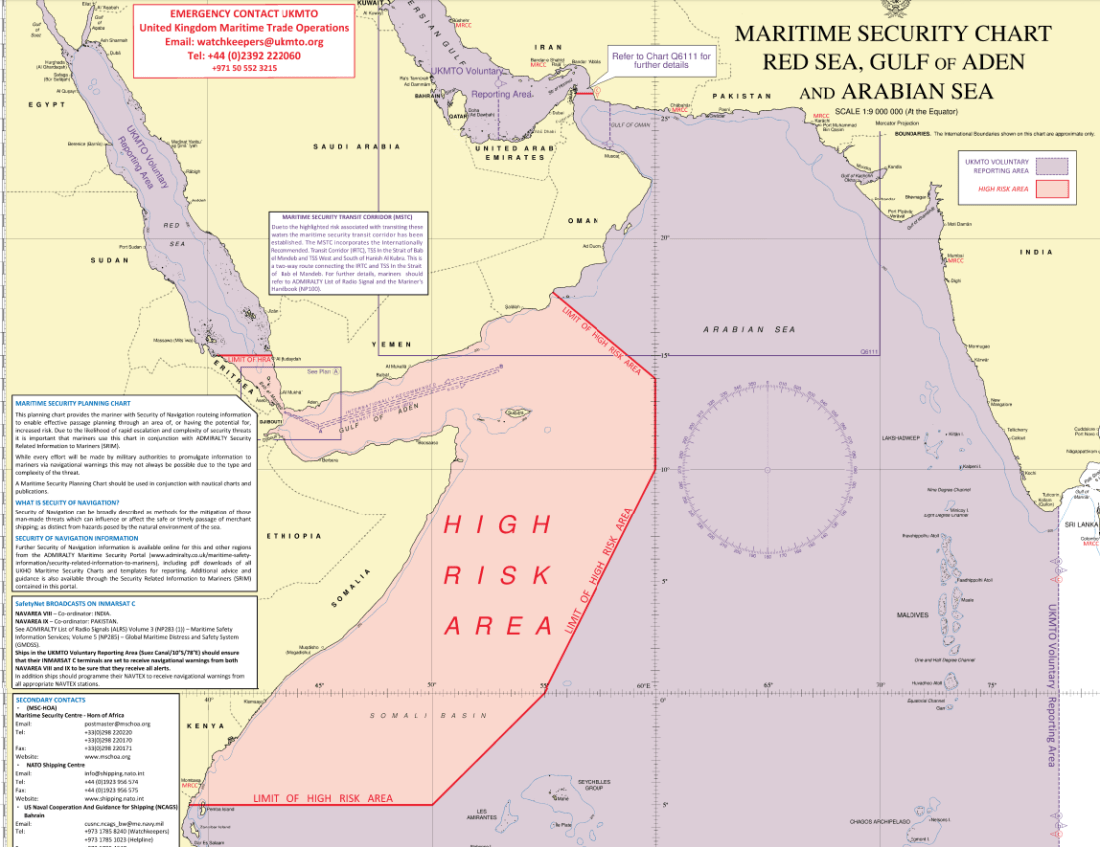
“FO TAHAFFUZ was conducted to support Combined Maritime Forces (CMF)’s overall campaign objectives of deterring suspected pirates from re-commencing their operations in the region,” said Chief of Staff to Commander CTF 151, Captain Adnan Laghari of Pakistan Navy. “Although the FO is now concluded, we still encourage all merchantmen plying through the Gulf of Aden to keep following the Best Management Practice BMP5 guidelines, and using the Internationally Recognized Transit Corridor for their safety.”
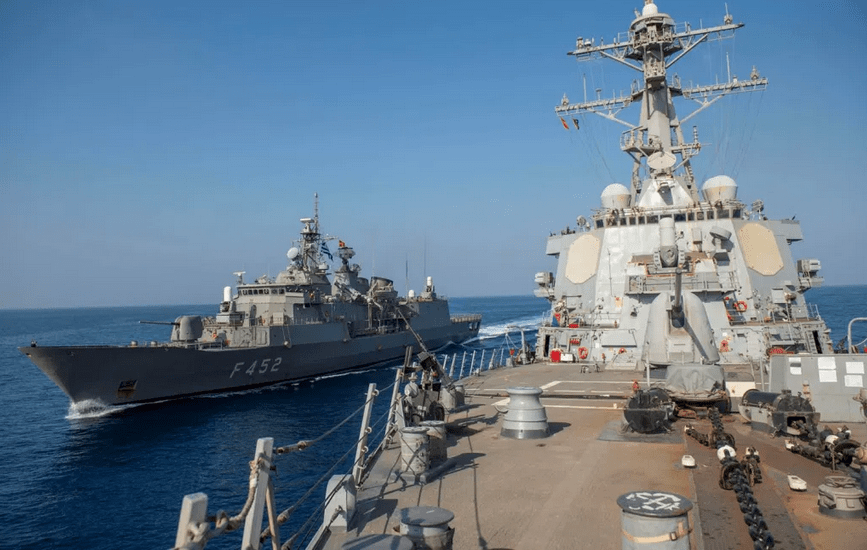
In addition to Pakistan Navy, the US Navy, Japanese Maritime Self-Defense Force, Hellenic Navy, Spanish Navy, and European Union Naval Force Somalia (Operation ATALANTA) all supplied their assets to the operation. The Canadian detachment of Unclassified Remote-Sensing Situational Awareness system also supported the Intelligence, Surveillance and Reconnaissance effort and contributed Pattern of Life assessments to the task force.
There was also a significant effort from the Djibouti and Yemen Navies and Coast Guards and the Royal Navy of Oman, who contacted merchant vessels sailing through the area, alerting them to the presence of warships through Maritime Awareness Calls.
Finally, the United Kingdom Maritime Trade Operations (UKMTO) office in Dubai, Marine Operation Centre in Djibouti, Maritime Security Centre – Horn of Africa, Maritime Security Centre at Oman and Joint Maritime Information Coordination Centre in Pakistan all provided additional contributions to the operation, alerting merchant shipping to expect an increase in military activity and ensuring swift sharing of information between all maritime stakeholders.
And the military activity was not just limited to the sea; maritime patrol aircraft and helicopters from both CMF and EUNAVFOR provided overwatch across the Gulf of Aden and off the Somali coastline.
“The goal of FO TAHAFFUZ is to show presence, reassure merchant and fishery communities and improve understanding of local Patterns of Life. The FO has significantly enhanced interoperability between regional counter-piracy forces, and hence contributed to build regional counter-piracy capability.” Commodore Abdul Munib of Pakistan Navy, Commander of CTF-151 said.
Through constant cooperation between CMF nations and partners, CTF-151 has for many years helped to maintain the integrity of vital lines of communication and successfully mitigated the risk of piracy in the area of Gulf of Aden and Somali Basin, especially through strategic waterways such as the Bab-el-Mandeb.
The Gulf of Aden is of immense importance to maritime trade as the main shipping lane between the Indian Ocean and the Mediterranean Sea. With the monsoon season fading, and sea conditions becoming favourable for sailors, there has been a large increase in the number of small fishing vessels, skiffs and dhows in operation close to the coastlines of neighbouring states.